Why Risk Management?
Companies should invest in risk management and cybersecurity to safeguard their valuable assets, protect their reputation, comply with regulations, and avoid costly breaches that could disrupt operations and harm their customers.
As a Managed Services Security Provider (MSSP), we specialize in enhancing the security of your technology implementations. Our security infrastructure services cater to diverse needs, making us a versatile choice for organizations.
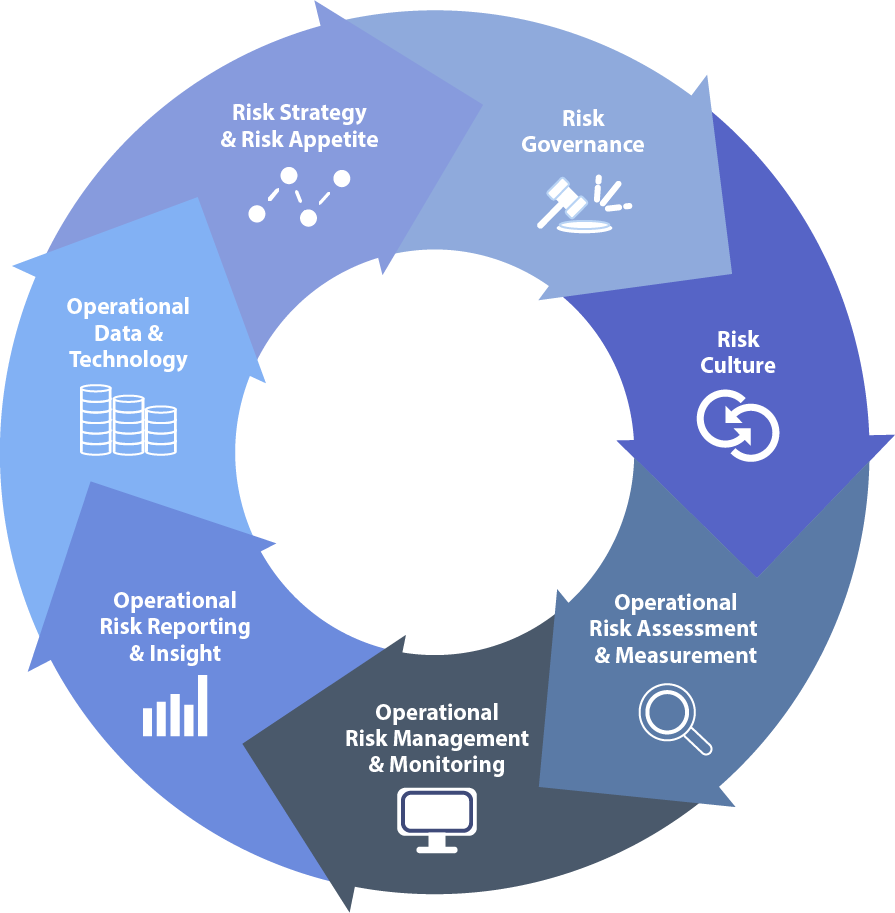
Risk Management Framework
When organizational security and privacy is top-of-mind, a risk management framework approach can be the most effective, efficient defense. Allow Digital Charter to meet the challenge of cyber supply risk management with their NIST recommended solution.
Prepare: Essential activities to prepare the organization to manage security and privacy risks
Categorize: Categorize the system and information processed, stored, and transmitted based on an impact analysis
Select: Select the set of NIST SP 800-53 controls to protect the system based on risk assessment(s)
Implement: Implement the controls and document how controls are deployed
Assess: Assess to determine if the controls are in place, operating as intended, and producing the desired results
Authorize: Senior official makes a risk-based decision to authorize the system (to operate)
Monitor: Continuously monitor control implementation and risks to the system
Practice Areas
Satisfied Customers
We team with industry leaders for greater innovation